In 2026, digital fraud has evolved far beyond the poorly written "Nigerian prince" emails of the past. Today's scammers deploy sophisticated artificial intelligence, voice cloning technology, and psychological manipulation tactics that can deceive even the most cautious individuals. As a private investigator in California with over 30 years of federal law enforcement and military JAG experience, Living Waters Investigation and Protection has witnessed firsthand how these schemes devastate families, drain bank accounts, and compromise sensitive personal information.
The cost of digital fraud in the United States now exceeds $10 billion annually, yet the majority of victims never report these crimes due to embarrassment or the belief that nothing can be done. This article dissects the anatomy of modern scams: from AI voice clones to "smishing" (SMS phishing): and provides actionable red flags the public must recognize. More importantly, we explain why professional verification through experienced legal investigations in CA remains your most effective defense against these evolving threats.
The Evolution of Digital Deception: Understanding Today's Threat Landscape
Modern fraud operates on multiple fronts simultaneously, utilizing technology that was unavailable just five years ago. Fraudsters now create synthetic identities: fabricated personas combining real stolen data (such as Social Security numbers from data breaches) with falsified information. These synthetic identities bypass traditional verification systems because they contain enough legitimate data points to appear authentic.
AI-generated voice clones represent one of the most alarming developments in fraud technology. Scammers can now replicate a family member's voice using as little as three seconds of audio scraped from social media videos. Victims receive calls from what sounds exactly like their grandchild or child, claiming to be in an emergency and urgently needing money wired immediately. The emotional manipulation, combined with technological sophistication, creates a perfect storm of vulnerability.
Automated bot attacks continuously probe systems for weaknesses, testing millions of stolen credential combinations per hour. When these bots identify a vulnerability, human operators take over to maximize the exploitation before detection occurs.
The Anatomy of Common Scams: What You Need to Recognize
AI Voice Clone Scams ("The Grandparent Scam 2.0")
How It Works: Fraudsters research your family through social media, identify vulnerable targets (often elderly relatives), and deploy AI-cloned voices during carefully timed calls. The caller claims to be a grandchild in legal trouble, a hospital emergency, or stranded abroad, always demanding immediate wire transfers or gift card purchases.
Red Flags:
- Urgent demands for immediate action without time to verify
- Requests for unconventional payment methods (wire transfers, cryptocurrency, gift cards)
- Instructions not to contact other family members
- Caller ID spoofing showing a familiar name or number
- Pressure to keep the "emergency" confidential
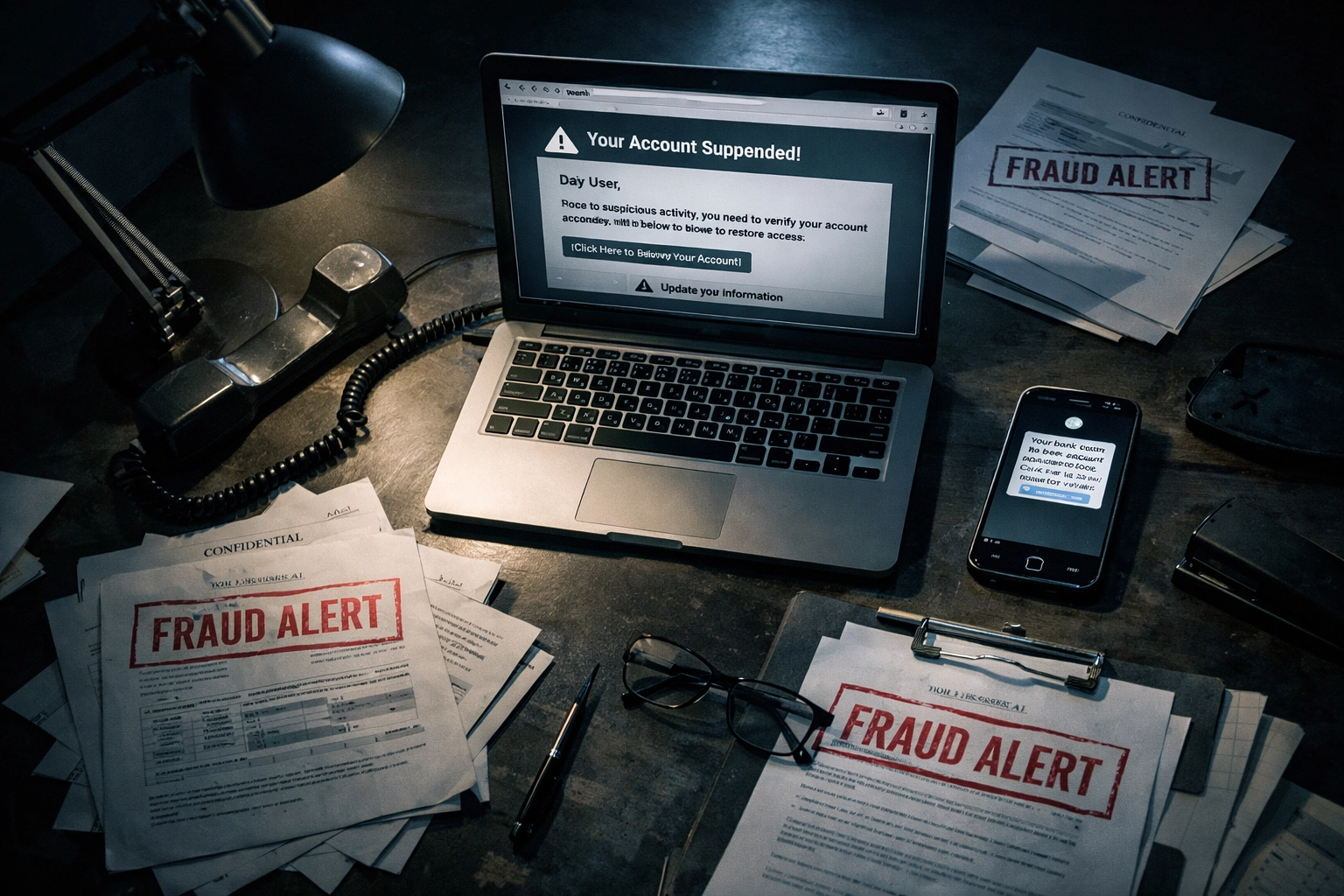
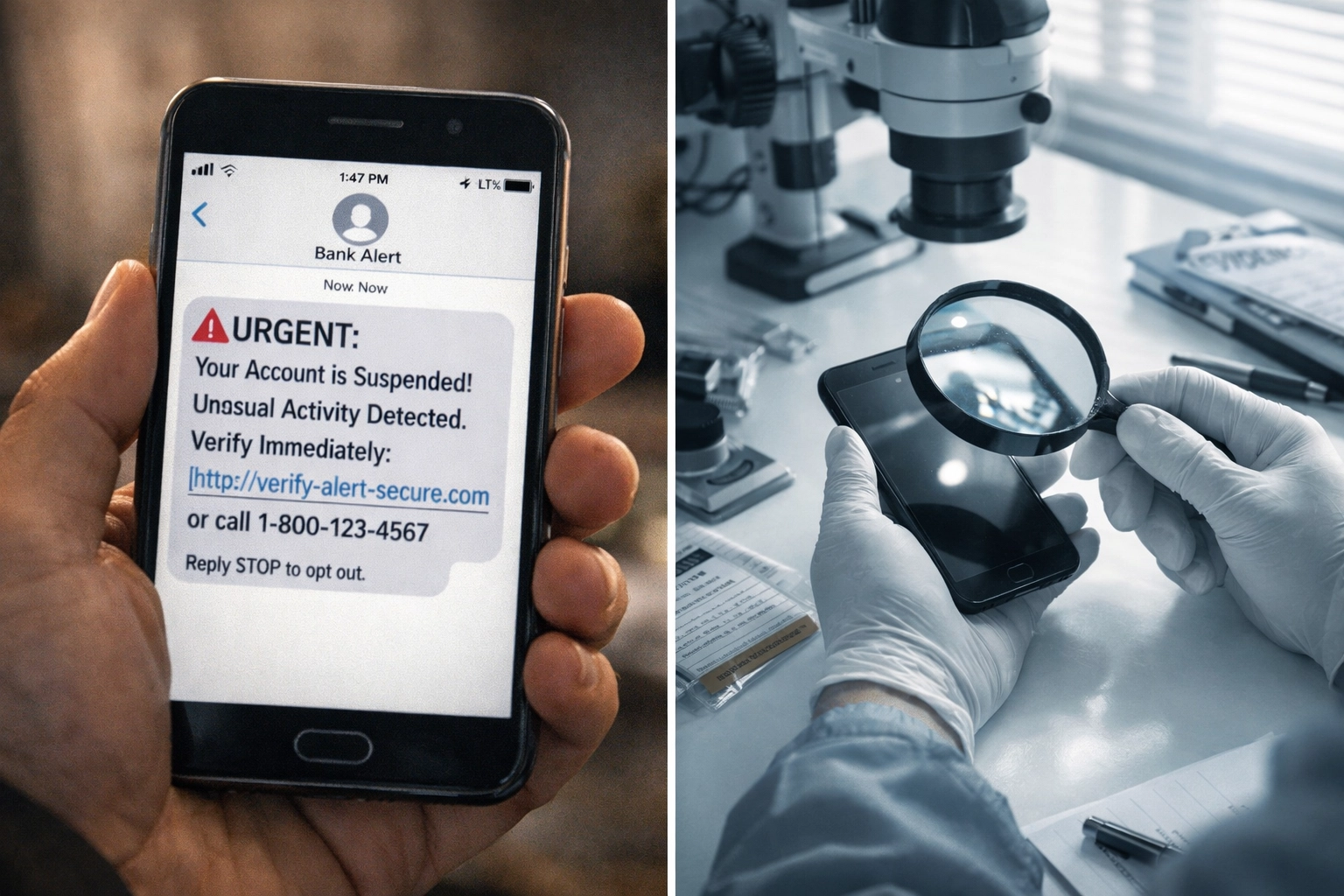
Smishing (SMS Phishing)
How It Works: Text messages impersonating banks, government agencies, or delivery services direct victims to click malicious links or provide sensitive information. These messages often create artificial urgency ("Your account will be frozen") or exploit anticipation ("Your package cannot be delivered").
Red Flags:
- Unexpected verification codes or password reset messages you didn't request
- Generic greetings ("Dear Customer") from institutions that know your name
- Shortened URLs or links with misspelled domain names
- Requests to "verify" account information via text
- Threats of account suspension or legal action
Email Phishing and Business Email Compromise
How It Works: Sophisticated phishing emails now replicate legitimate corporate communications with near-perfect accuracy. Business Email Compromise (BEC) specifically targets companies, with fraudsters impersonating executives to authorize fraudulent wire transfers or redirect payroll deposits.
Red Flags:
- Slight variations in email addresses (john@company.com vs. john@companny.com)
- Requests to update direct deposit information
- Unusual urgency from supervisors requesting financial transactions
- Attachments or links from unexpected sources
- Grammar and formatting inconsistencies, despite professional appearance
Why Professional Verification Outperforms DIY Efforts
The average individual lacks access to the databases, investigative techniques, and verification protocols necessary to authenticate sophisticated fraud attempts. What appears legitimate on the surface often reveals inconsistencies when examined through professional investigative methods employed by a private investigator in Riverside or throughout California.
Real-Time Authentication and Cross-Verification: At Living Waters Investigation and Protection, our verification process validates information across multiple independent sources simultaneously. We cross-reference phone numbers, email addresses, IP addresses, physical locations, and identity documents against proprietary databases unavailable to the general public. This multi-parameter authentication detects discrepancies that single-source verification misses.
Continuous Risk Monitoring: Identity verification represents an ongoing process, not a one-time check. Our investigative protocols include continuous monitoring for suspicious pattern changes, unusual account activities, and emerging threats specific to our clients' risk profiles. This proactive approach identifies fraud attempts before financial or reputational damage occurs.
AI-Powered Anomaly Detection: Leveraging advanced machine learning algorithms refined through decades of federal law enforcement experience, our team analyzes vast datasets to identify anomalous patterns human review would overlook. Unlike static rule-based systems relying on predefined triggers, our adaptive protocols evolve alongside emerging fraud techniques.
Organizations implementing robust professional verification report fraud reduction approaching 90%, with verification times reduced from weeks to seconds: a critical advantage when scammers pressure victims to act immediately.
The Living Waters Advantage: Veteran-Led Expertise Applied to Modern Threats

As a veteran-owned investigation firm with backgrounds in federal law enforcement and military JAG operations, Living Waters brings institutional knowledge and investigative discipline to every case. Our 30+ years of combined experience spans complex fraud investigations, identity verification protocols, and asset identification: capabilities directly applicable to protecting clients from digital fraud.
Bilingual Services for California's Diverse Communities: Fraud does not discriminate by language, and neither should protection services. Our bilingual private investigator team provides comprehensive services in both English and Spanish, ensuring California's diverse communities receive the same level of professional verification and fraud investigation. We conduct consultations, interviews, and reporting in the client's preferred language, handled with absolute discretion and cultural sensitivity.
24/7 Availability: Fraud operates around the clock, and so does our response capability. When you suspect a scam or require immediate verification, our team remains accessible 24 hours a day, 7 days a week. Time-sensitive situations demand immediate professional intervention: delays can mean the difference between preventing fraud and attempting recovery after the fact.
Confidentiality and Discretion: Every investigation is conducted with strict confidentiality protocols. Whether verifying a potential romance scam, investigating suspected business fraud, or authenticating communications purportedly from financial institutions, we ensure absolute discretion throughout the investigative process.
When to Engage Professional Verification Services
Certain situations warrant immediate professional investigation rather than self-verification attempts:
- Unexpected inheritance notifications or lottery winnings from foreign sources
- Romance scam suspicions when online relationships quickly progress to financial requests
- Business email compromise involving unusual wire transfer requests from executives
- Employment offer verification requiring upfront payments or personal information before hiring
- Investment opportunities promising guaranteed returns or requiring immediate decisions
- Voice or video calls from family members requesting emergency financial assistance
- Legal threats or arrest warrants demanding immediate payment to resolve
In these scenarios, the cost of professional verification represents a fraction of potential losses from successful fraud.
Actionable Steps: Protecting Yourself and Your Family
While professional verification provides the most comprehensive protection, implement these immediate safeguards:
- Establish family code words for emergency communications that only legitimate family members know
- Enable multi-factor authentication on all financial and email accounts
- Never click links in unexpected text messages or emails; navigate directly to official websites
- Verify independently before acting on urgent requests: call known phone numbers, not those provided in suspicious communications
- Review privacy settings on social media to limit information available to scammers
- Monitor financial statements weekly for unauthorized transactions
- Register for credit monitoring to detect identity theft attempts early
- Document everything if you suspect fraud: preserve emails, texts, call logs, and communications
Professional Investigation Services Available
Living Waters Investigation and Protection offers comprehensive fraud verification and investigation services throughout California:
- Identity Verification and Authentication
- Romance Scam Investigation
- Business Email Compromise Analysis
- Asset Searches and Recovery Investigations
- Background Verification for Online Relationships
- Due Diligence Investigations for Investment Opportunities
- Missing Persons Located Through Fraud Schemes
Each investigation is customized to the specific circumstances, conducted with professionalism at every step, and delivered with actionable intelligence you can trust.
Conclusion: Professional Verification as Prevention
Digital fraud will continue evolving, deploying increasingly sophisticated technology to exploit human vulnerabilities. The question is not whether you will encounter fraud attempts, but whether you will recognize them before suffering losses.
Professional verification through experienced investigators transforms uncertainty into clarity. At Living Waters Investigation and Protection, we apply decades of federal law enforcement expertise, veteran discipline, and advanced investigative technology to protect California residents and businesses from digital fraud. Our bilingual team stands ready 24/7 to provide the verification, investigation, and peace of mind you deserve.
If you suspect fraud, require verification of suspicious communications, or need professional investigation services, contact Living Waters Investigation and Protection for a confidential consultation. We serve clients throughout California with absolute discretion and unwavering commitment to uncovering the truth.
Living Waters Investigation and Protection
Veteran-Owned | Bilingual Services | 24/7 Availability
Contact Us
Protección profesional. Resultados confiables. Servicio bilingüe disponible.

